Free the Ring
I have to cut my videos into highly refined and compact information bombs.
I don’t know if the info-attack rhythm works well for my viewers or if everyone’s brain is just TikTokified, but you rarely get to see my many project-failures simply because they’re not really important enough to make the final cut.
In the case of my recent smart camera video, I spent hundreds of hours diving deep into the technical functionality and security of Ring’s ecosystem of cameras. One of those challenges that didn’t make the final cut was inspired by FULU, a non-profit run by Louis Rossmann that raises bounties for those who manage to “hack” their own devices to free their functionality. Naturally, they have a bounty for the challenge of allowing someone to use their Ring camera hardware without Amazon’s servers in an accessible way.
The bounty terms have eased up a bit, as the original conditions were frankly nuts. I don’t blame FULU for this as you can’t really understand how unrealistic the terms are until you start prodding around the cameras themselves. But I was more interested in answering my own technical questions than I was interested in collecting a bounty, so this didn’t bother me.
I personally don’t want to look at another Ring camera for the rest of my life after the last 2 months, so this post is to potentially help to anyone trying their hand at this bounty.
The good and bad news is that Ring has exceptionally good hardware security. This is great if someone steals your doorbell camera. This is terrible if you want to use your doorbell camera without Ring’s cloud-services.
The most promising candidate in the ecosystem that I had was the Ring Indoor Gen 2.
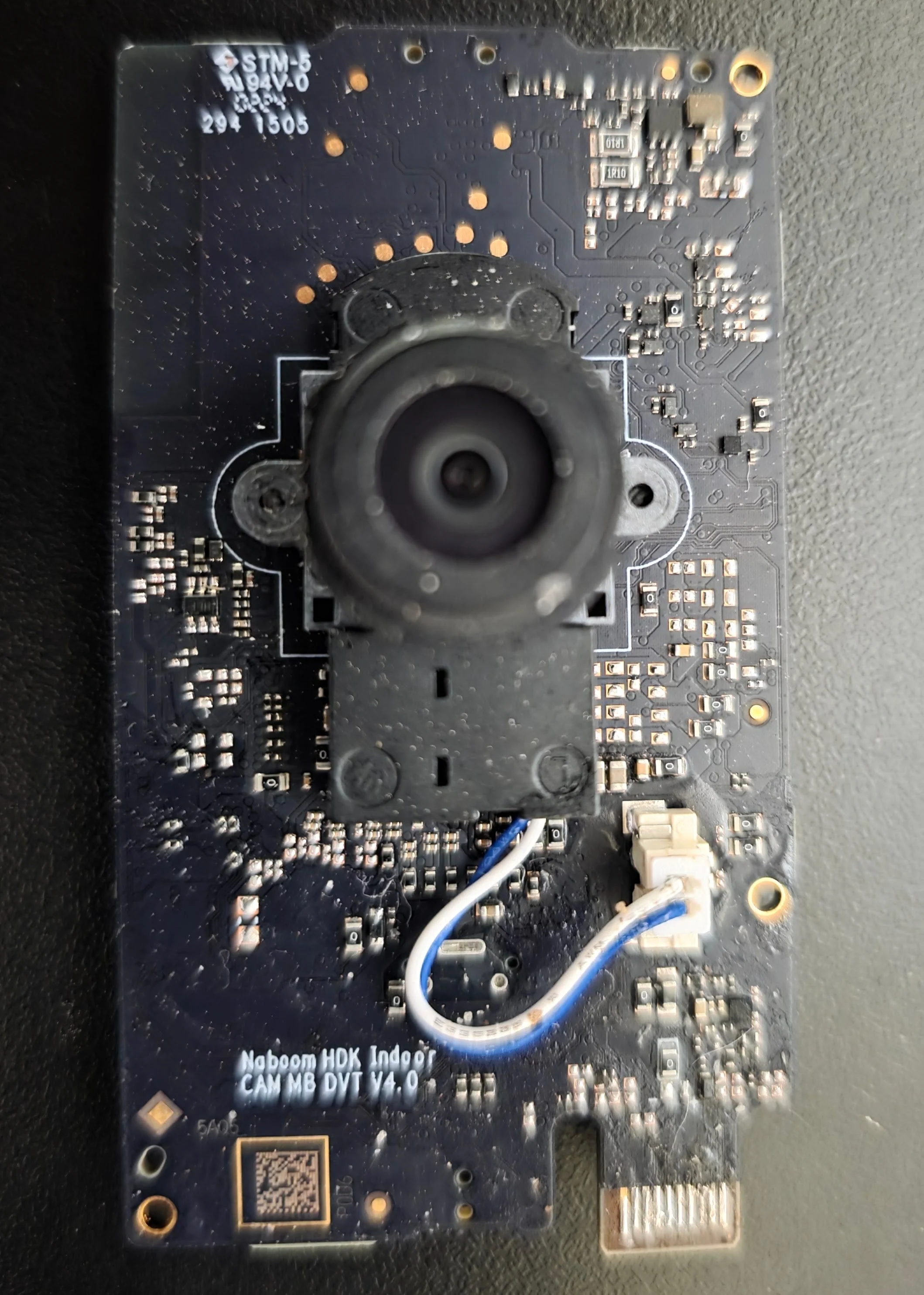
When popped open, you’ll be greeted by a Naboom HDK Indoor Cam motherboard. Don’t get too excited, this PCB is made specifically for Ring and isn’t used on other more consumer-friendly camera models.
Do yourself a favor and remove the speaker by unplugging the tiny pin cable. It’s extremely magnetic and fragile.
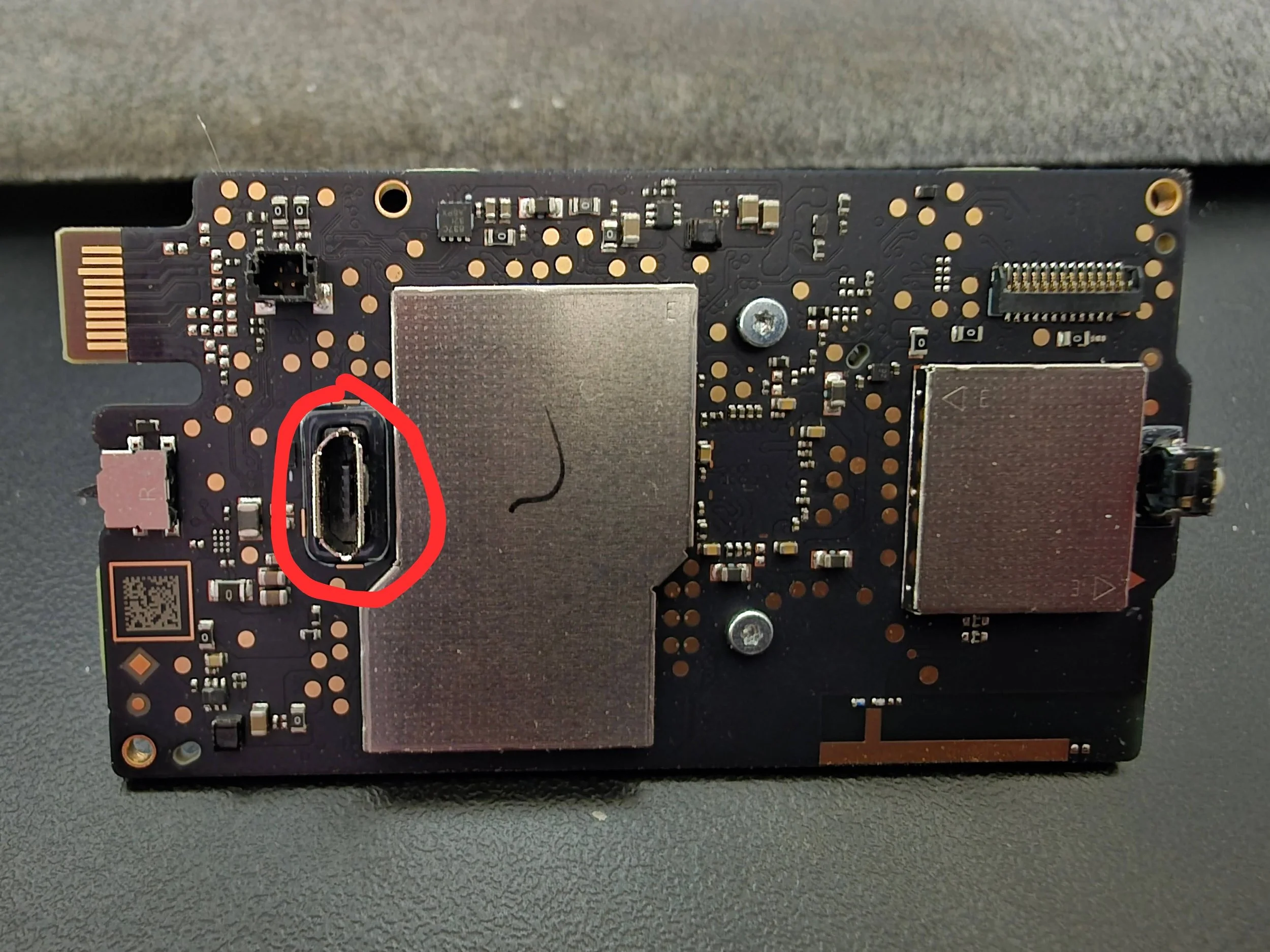
Hey look! It has a micro-usb port!
…that does literally nothing with data (or perhaps until it’s activated in the firmware).
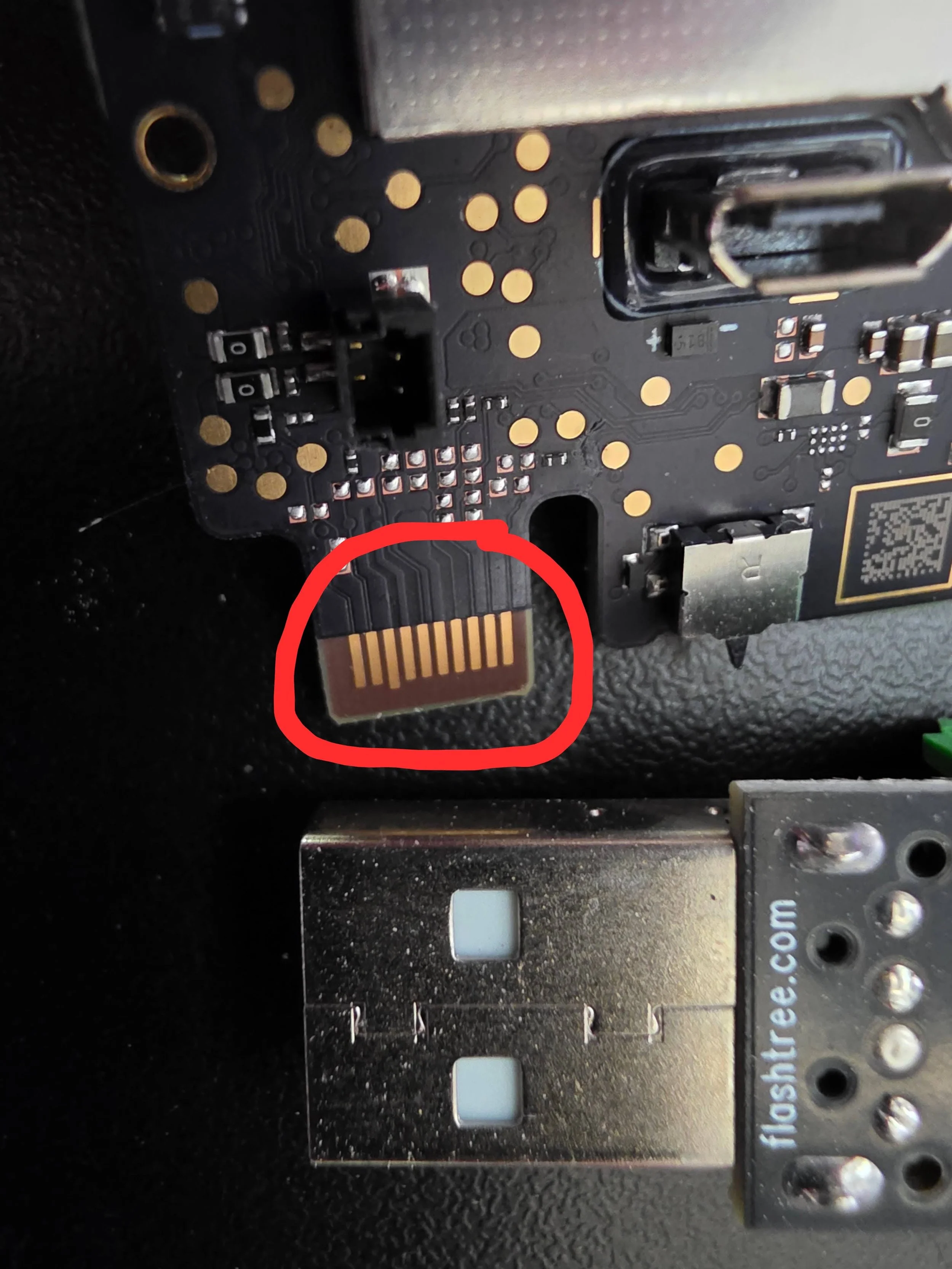
You’ll notice a very tiny 20-pin proprietary connector. This is your ticket. I assume that the technicians at Ring or Naboom have a nice cable that plugs into this.
Unfortunately you do not have this cable, and the majority of my time was spent trying to find or prototype my own. It’s either an FPC ZIF connector or a specialized docking cradle.
This connector type is called “gold fingers”.
It’s a 20-position card-edge configuration with 10 pins per side. The width from the left edge of pin 1 to the right edge of pin 10 is 3.5mm, which suggests a 0.4mm pitch in the 9 pin gaps.
I had ordered connectors from China that had the specs to fit, but what I was sent was a few fractions of a millimeter off. I did this a total of 3 times before realizing that I’d have to bring my torn-apart Ring camera to Guangdong and start jamming it into things at factories.
So I turned on my microscope, drank a lot of whiskey to calm my fidgety nerves, and soldered the night away.
4 Ring cameras died tragic deaths that night. Well, the UART (if we’re assuming it’s UART) ports died, at least. That’s where I left it as the challenge calls for an accessible solution, and if I can’t solder the 20-pins without burning the board in my lab with professional-grade tools, then a tech-novice isn’t going to be able to convert their Ring cameras for home use.
But if you do manage to do this, you’re going to be cracking a password at some point. I was looking forward to this part, but that also meant that I couldn’t include it in my video because this is a scary gray area. The silly old CFAA crimilizes “unauthorized access”. You own the Ring camera, so it can be argued that you have the legal authority to bypass its security. But what then? Can you be sure that the camera will not try to connect to Ring’s services once the WiFi radio is turned on? You’ll have to setup a sandbox network to be sure if you want to publicly share your findings.
Finally, all of this is certainly violating the EULA you agreed to if these cameras were ever activated on your property. This could make you liable for civil damages. Welcome to the insane asylum that is cybersecurity research. This is just the first ward for out-patients.
Chk chk. Naboom!
This is your ticket. (USB A on the bottom for size-comparison).
Micro-USB for power.
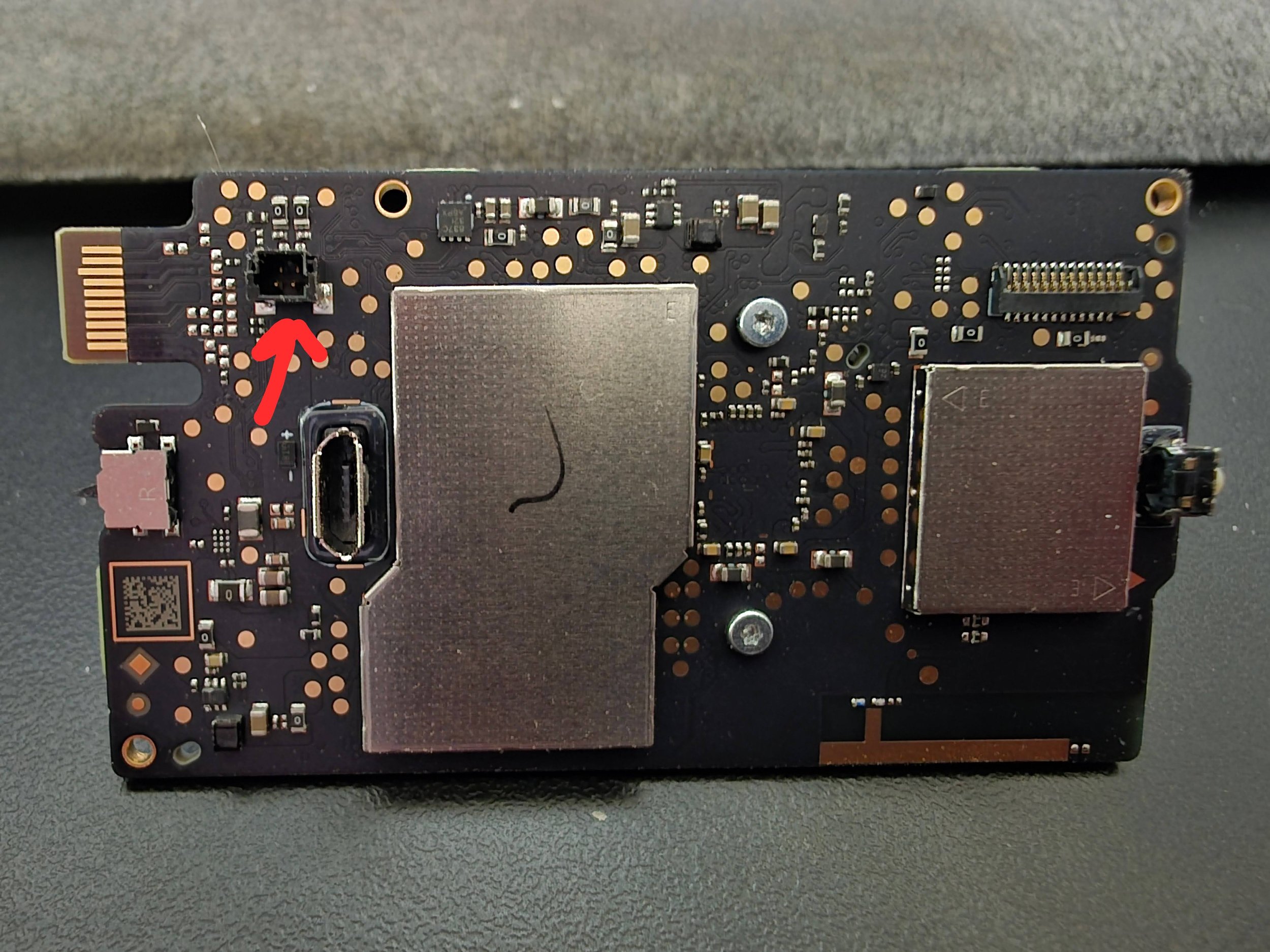
This is where the fragile speaker connects. Disconnect it before anything else.